Overshadowed by the release last week of the U.S. intelligence community’s assessment that Russian cyber attacks had indeed been aimed at our 2016 national elections, another report from the U.S. Dept. of Energy (DOE) revealed even more disturbing vulnerabilities in the country’s electricity grid.
Released January 6, the DOE’s 494-page Quadrennial Energy Review concluded that the national grid in its current state “faces imminent danger” from cyber attacks. “Cyber threats to the electricity system are increasing in sophistication, magnitude, and frequency,” it noted. “The current cyber security landscape is characterized by rapidly evolving threats and vulnerabilities, juxtaposed against the slower-moving deployment of defense measures.”
Taken together, the reports give an unsettling cyber start to the new year that has left many U.S. cities, utilities, AEC firms, and others both in and out of government feeling anxious, to say the least. They are asking what new steps, if any, they should be taking to ensure their collective cyber security in 2017.
“The current cyber security landscape is characterized by rapidly evolving threats and vulnerabilities, juxtaposed against the slower-moving deployment of defense measures.”
“Securing our physical infrastructure from hacking — a broader category, generally, but it encompasses AEC — may be the most pressing security matter of the next few years,” says John Tolva, former chief technology officer for the City of Chicago and now cofounder of Denver-based CityFi. Launched last summer, the start-up is an advisory-services platform for “urban change management,” aimed at helping cities “to leverage current and new technology” to “create positive, sustainable change.”
In the AEC industry, as well as the general public, heightened cyber fears date back to the infamous hack of 40 million Target customers in December 2013. Their data was presumably accessed via the poorly secured computer system of a Target vendor, a mechanical subcontractor. That well-known incident subsequently spawned a surge in cyber security insurance and other protective offerings from lawyers, insurers, and related vendors. Last fall’s revelations by Yahoo of even more massive data breaches has only added to the general sense of concern.
“It’s a quickly emerging issue, especially now, so we are definitely getting more questions about it from owners,” says Raj Gupta, CEO of Chicago’s Environmental Systems Design, a 50-year-old engineering firm focused on creating more intelligent, efficient buildings. “That (2005) book, The World Is Flat, talked about how everything is connected now,” he adds. “But it also noted that the ‘bad guys’ can do some terrible things.”
With that in mind, “our members are very worried about cyber security,” says C. Fara Francis, CIO of the Associated General Contractors of America (AGC). In November, the AGC-IT Forum provided a four-part CyberSecurity Webinar Series for its national membership. Contractors “recognize that this should be a business and strategic concern, not just an IT concern,” Francis says. “So, they are working on deploying this approach within their companies.”
Managing fears, risks
Part of that approach now involves cyber liability insurance, which “is a huge growth area in the U.S.,” says Steve Holzer, an AEC Hackathon board member and the new director of knowledge management for St. Louis-based BIMobject North America, a Swedish-owned BIM supplier. However, he is skeptical of the need for such policies. “Pure hype,” says Holzer. “Cyber security is a salacious topic that imparts fear and panic because so few have any idea what it is. But so little, if anything, has ever actually been accomplished as a result of being ‘hacked,’ other than maybe an airplane ticket to Barcelona showing up on your Visa card. The damages are nil.”
Even the celebrated Target case only resulted in $10 million being awarded in claims, “and $6.5 million of that went to the lawyers,” Holzer says.
“Our industry should be diligent with protecting itself from outside hacks — which are highly unlikely but still possible — but be much more concerned about the enemy within.”
AEC Hackathon founder Paul Doherty, AIA, also president and CEO of The Digit Group (TDG), Memphis, TN, agrees. “I really don’t see the need to purchase insurance because there has not been a legal claim against any AEC firm for not having a cyber security plan, coverage, etc.,” he says. “It’s an immature overreaction to a nonevent, so the underwriting and premiums would be difficult to purchase at this point. Our industry should be diligent with protecting itself from outside hacks — which are highly unlikely but still possible — but be much more concerned about the enemy within. [Edward] Snowden taught us all this valuable lesson. It’s a two-front war.”
Toward that end, Doherty says that AEC firms should be more worried about “the loosey-goosey attitude many firms have about securing their own data internally and among consultants on projects… The more interesting question is which of your employees may already be leaking info to competitors, or to themselves to help start their own firms, or storing company data off-site or on personal devices.”
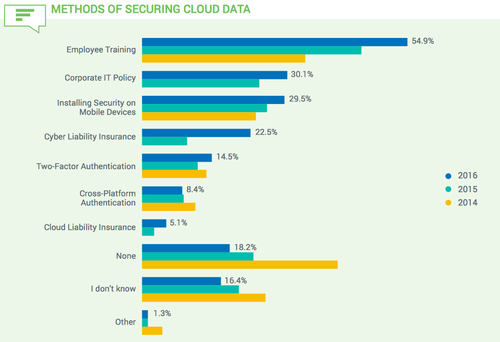
Such internal and external pressures no doubt have contributed to the surge in cyber insurance. According to the JBKnowledge 2016 Construction Technology Report, released in December, which surveyed 2,600 industry IT professionals: “Cyber liability coverage [has] more than doubled since 2015, and those that are not using cloud security methods [have] dropped by half since 2014. Employee training continues to be the most frequent data security method used, most likely because it is the least expensive and is often the ‘easiest’ to implement. These results show that more construction firms are understanding the need to implement cyber security defenses to protect sensitive data available in the cloud.”
To put their minds at ease, JBKnowledge CEO James Benham does recommend that contractors buy insurance. As he told attendees last spring at BuiltWorlds’ inaugural CEO Tech Forum, “if you invest in a cyber liability policy, the insurance company will even send out trainers to your business to help teach your employees and vendors proper practices.”
Benham also referred all to visit CloudSecurityAlliance.org for a preliminary checkup.
Even so, taking precautions is surely advisable. But we shouldn’t kid ourselves, warns Holzer.
“At the end of the day, a good hacker can get into anything,” he says.


Discussion
Be the first to leave a comment.
You must be a member of the BuiltWorlds community to join the discussion.